A network risk assessment looks at how each of these devices such as computers laptops iPads servers routers etc are managed. Lets take a look at how performing a risk assessment and analysis can be your strongest defense.
A Complete Guide To The Risk Assessment Process Lucidchart Blog
Perform risk analysis for your home network.

. This is necessary to further analyze system boundaries functions system and data criticality and sensitivity. 612 of WFH-RO IP addresses that have one or more services open have an exposed cable modem control interface either through the TR-069 TR. Think of probable sources of data leaks possible unauthorized access and untrustworthy authorized personnel.
To identify your vulnerabilities you can utilize information from any previous audits and government. Compact and easy to use. By identifying the security loopholes and weak spots in your network you can avoid breaches and attacks.
Perform risk analysis for your home network. In this live webinar IT security expert Jay discusses how to identify the security risks in your network and provides actionable tips to eliminate the risks. Here is an example.
Visualize hop-by-hop analysis of cloud or on-prem applications or services. Each issue is given a score of 0 to 100 and combined into an overall issue score. For each threatvulnerability pair determine the level of risk to the IT system based on the following.
Consists of that process data. Prepare a disaster recovery plan for your home net work. Risk Report NETWORK ASSESSMENT PROPRIETARY CONFIDENTIAL PAGE 6 of 18 Recommendation.
Step one of performing a cybersecurity risk analysis is to catalog all your businesses network resources. Document every device including computers tablets routers printers servers and phones on the network. Some of these devices have compliance modules that the assessment picks up such as PCI and HIPAA compliance.
Think of a network risk assessment as a baseline or snapshot of your network security. Before you can start assessing risk you need to review network resources. Threat Vulnerability Asset Impact Likelihood Risk Control Recommendations High- System Failure- High- Computers are all old Critical- Laptop Computer Critical- All activites High- Operating System is not supported High- Potential Loss of 4k per occurrence Buy a new pc 1500 cost.
The likelihood that the threat will exploit the vulnerability. Once you have identified your digital assets you must think about what threats put your network security at risk and how vulnerable your assets are to them. Anti-virus not turned on 92 pts each 92 Current Score.
The system provides. Viruses can corrupt your files and delete valuable data negatively impacting your daily operations. Identify and Prioritize Assets.
252 of WFH-RO IP addresses have one or more services exposed on the Internet. This part of the assessment should really be done by a professional but its still. Prepare a disaster recovery plan for your home net work.
At their worst viruses have the potential to wipe clean your entire hard drive. The first step to building an efficient security strategy is to perform risk assessment. Assets include servers client contact information sensitive partner documents trade secrets and so on.
What follows is an issue summary from a real network assessment we performed. Compact and easy to use. When a network risk assessment is performed all of the devices on your network are examined and analyzed.
Without knowing your weaknesses protecting against them will be next to impossible. Research antivirus and antispyware software that you can purchase for your home network. Now lets look at what steps need to be taken to complete a thorough cyber risk assessment providing you with a risk assessment template.
1 The first and most important action we can take is to configure Windows to perform automatic updates this will ensure we have the latest patches and updates installed. What Are the Benefits. To estimate risk value the most straightforward method is to calculate the probability of the event occurring and multiply it by the cost of the event.
Get Flexible Deployment Options to Make Purchasing Managing Your Software Easy. Disable or remove user accounts for users that have not logged in in 30 days. We were unable to determine if an anti-virus software is enabled and running on some computers.
92 pts x 1 92. The approximate cost of each of these occurrences. Residential networks exhibit their own unique attack surfaces with regards to network perimeter security.
Lab-grade VNAs for IOT and Wireless. In this live webinar IT security expert Jay discusses how to identify security risks in your network and provides actionable tips to eliminate the risks. Software Vulnerabilities Pose Network Security Risks.
By identifying the security loopholes and weak spots in your network you can avoid breaches and attacks. Take inventory of systems and resources. As such its important to advise your staff to never open an email or click on a link they dont recognize.
Ad Powerful Network intelligence Software for on-premises cloud or hybrid environments. Ad The most affordable lab-grade VNAs. Prioritize the Information Security Risks.
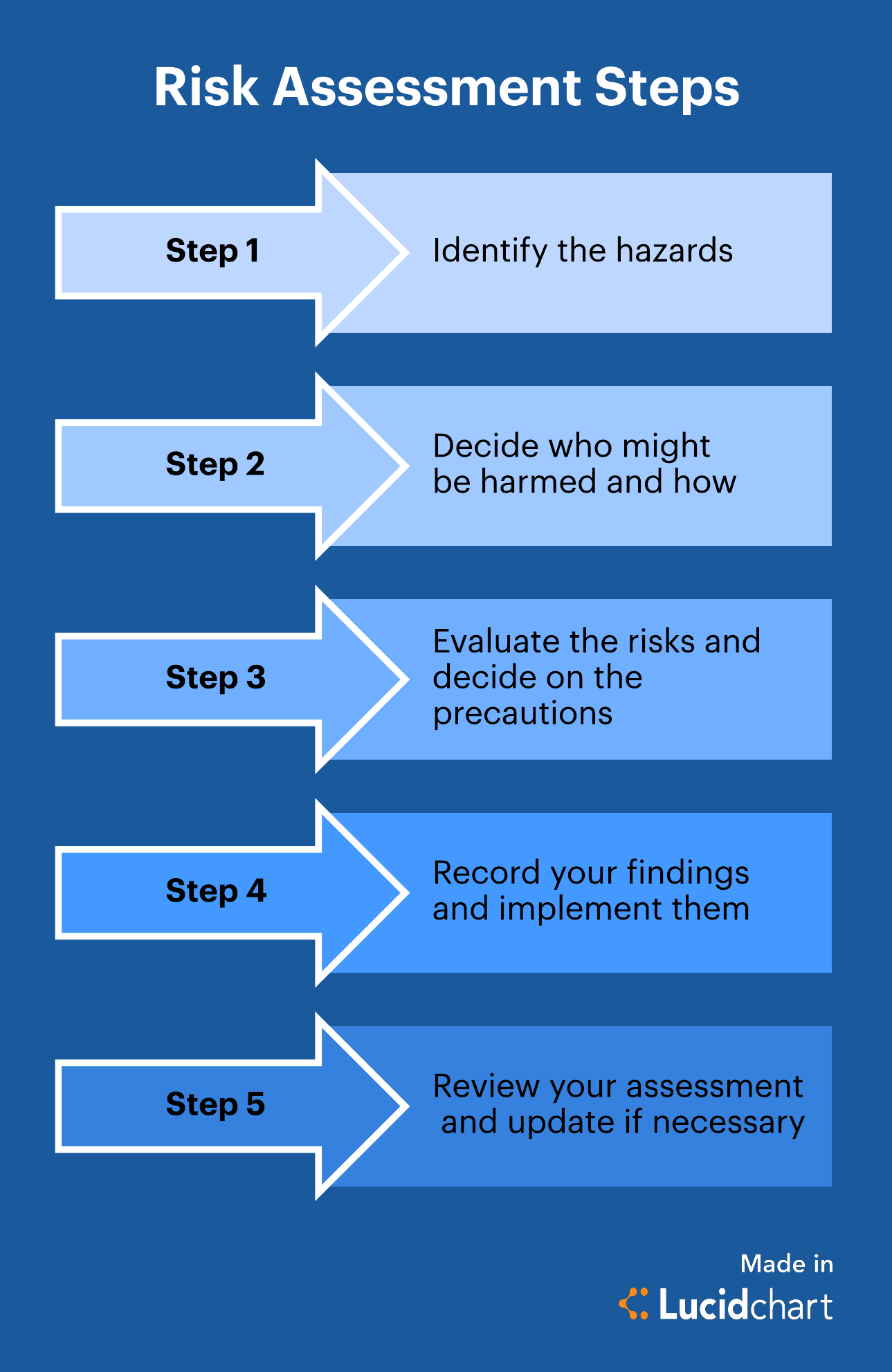
Unsupported Operating Systems 97 points. 5 Steps to Perform a Cyber Security Risk Assessment on Your Network Review Your Network Resources. Perform risk analysis for your home network.
Take the First Step by Conducting a Network Risk Assessment The reality is that you cant improve what you dont measure. Most organizations dont have an unlimited budget for information risk management so its best to limit your scope to the most business-critical assets. Lets say you want to assess the risk that the cost of a component of your product will increase substantially.
Remember what you as a technician think is valuable might not be what is actually most valuable for the business. Perform risk analysis for your home network. Risk value Probability of event x Cost of event Example.
A higher score equals higher risk. Now lets walk through the risk assessment procedure. Ad A Simple Interface to Work Across Multiple Data Sources and Easily Perform Risk Analysis.
Is located details on physical environment. Each network assessment is scored on best practices for network health performance and security. The first step to building an efficient security strategy is to perform risk assessment.

Take This Risk Management Course And You Ll See Your Struggles Literally Risk Management Risk Management Strategies Management

Here Is Our Pre Filled Out Part B Risk Assessment Form For Street Photography Assessment Writing Paper Template Risk Matrix

Financial Risk Assessment Template Inspirational Financial Risk Assessment Template Illwfo Network Infrastructure Report Template Assessment
0 Comments